Prevent XML External Entity (XXE) processing attacks
Many older or poorly configured XML processors evaluate external entity references within XML documents.
Security assessment
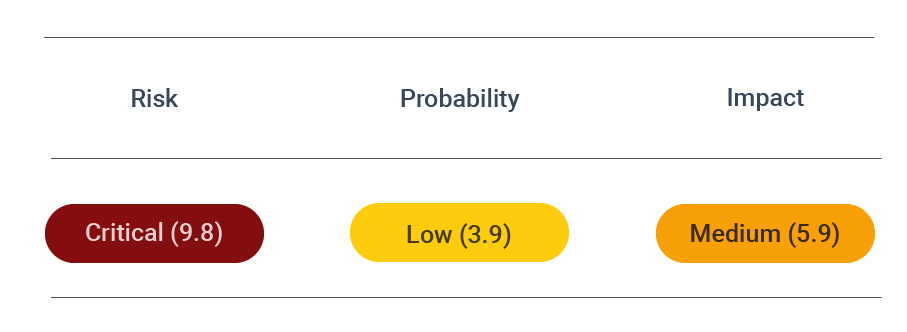
CVSS vector: AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:L/CR:H/IR:H/AR:H/MAV:N/ MAC:L/MPR:N/MUI:N/MS:U/MC:H/MI:H/MA:H
Vulnerability information
External entity profiles are defined by outside sources such as a file on a local computer or a web URL. Such entities ensure that the XML processor behaves consistently even when unexpected characters are parsed.
External entities have various legitimate use cases:
- Calling an XML document hosted locally to be used in another XML document
- Dividing documents into smaller, logical units
- Referring to the same entity framework multiple times without having to repeat the same element
- Using external entity references with different encoding in the same document
If the parser that processes external entities is weakly configured, hackers can intercept data going to the server and inject malicious payloads. Attackers typically also exploit custom external entities to access sensitive data.
What are XXE Attacks?
Some web applications include XML processors that evaluate untrusted external references within an XML file. These references enable attackers to use external parameter entities to disclose various configuration file information, which the attackers then exploit the system further.
Since these attacks occur through parsing XML inputs in an application, attackers can leverage it to access other integrated systems, leading to application unavailability and loss of sensitive data. It is, therefore, prudent to understand the nature of these attacks and how they can be prevented.
How To Fix XXE Attacks?
An XXE vulnerability exists when a web application parses XML documents from an untrusted source. If the underlying XML parser accepts DTD, an attacker can manipulate the XML document to allow him to read files on the system. For example, the following code snippet shows a malicious XML document that forces the application to read sensitive files on the server.
<?xml version="1.0" encoding="utf-8"?>
<!DOCTYPE credentials [
<!ELEMENT credentials ANY >
<!ELEMENT user ANY >
<!ENTITY user SYSTEM "file:///etc/passwd">]>
<credentials>
<user>&user;</user>
<pass>mypass</pass>
</credentials>
A poorly configured XML parser would read the file specified in the DTD and possibly display it to the attacker. Therefore, to protect your web application from this attack, you can disable the entity loader for the XML parser, as the snippet shows below.
libxml_disable_entity_loader(true);
To disable the entity loader, it is recommended to use a local static DTD and remove any other DTD included in the XML document.