Configure secure TLS
A correctly configured TLS encryption ensures that your users only get content from your web application that has not been tampered with and cannot be eavesdropped on. Learn here how you can secure your TLS configuration.
Security assessment
Based on the specific cipher suite, the values can differ from one to another. For the exact value of each cipher suite, see the table below.
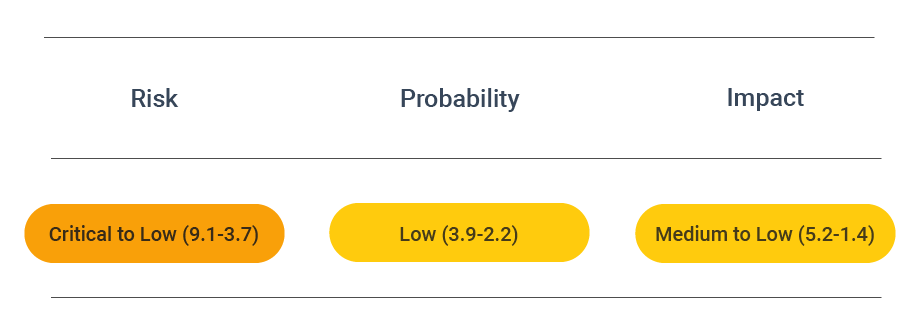
CVSS vector: AV:N/AC:H/PR:N/UI:N/S:U/C:L/I:L/A:N

About TLS
A correctly configured TLS encryption ensures that your users only get content from your web application. This means there is no unregulated tampering with the exchanged communication, and users cannot eavesdrop on through the Transport Layer Security protocol.
It is paramount to configure the Transport Layer Security protocol correctly to ensure the real security of your systems. If this is not done, this may create a sense of security that is not backed in reality.
One of the main aspects of TLS configuration is using suitable profiles. Internet organizations recommend profiles, and following them is a good practice.
Legacy profiles for TLS 1.1 and 1.0 have been found to have a lot of vulnerabilities. You should set up a migration plan to replace them with new versions.
Check TLS security settings for optimal security
In your TLS configuration, you should set the allowed Transport Layer Security protocol version and ciphers to the most up-to-date values, which are considered secure now.
First and foremost, it is essential to disable all older versions of the Transport Layer Security protocol, such as TLS 1.1 and 1.0. It is also a good idea to disable features that have proven to be insecure. More specifically, it is best to disable insecure renegotiation, insecure protocol downgrade, record compression, export key generation, and support for SSL 2.
As for TLS 1.3, it is advised not to use the zero round trip mode or 0-RTT. If it is enabled, clients can send data in a Transport Layer Security session before the complete TLS handshake. This can give way to replay attacks and other security vulnerabilities. So it is best to avoid 0-RTT mode unless application protocols have specific protection for replay attacks.
See the TLS configuration proposal offered by Mozilla or use the SSL Config Generator.
Secure a TLS configuration
For secure TLS configuration, it is crucial to use vital and trusted certificates.
Recommended server certificate configurations:
- Opt-in for the latest SSL/TLS protocol. Currently, modern versions 1.3 or 1.2 of the Transport Layer Security protocol exist.
- Check if you have any intermediate certificates. If you do, install them on your server so browsers get a full certification path.
- Ensure that your certificate applies to all of your hostnames.
- Use TLS implementations with AES cipher** variants rather than older versions with weak ciphers like DES.
- Opt-in for TLS Session Resumption to skip constant session key renegotiation.
- Enable Forward Secrecy (FS), also known as Perfect Forward Secrecy (PFS), to protect past session keys in case a private key is compromised.
- Select secure cipher suites. Recommended cipher suite requirements are a minimum of 128-bit encryption.
Prevent attacks
To configure the SSL/TLS encryption for your Apache and Nginx web server.
Apache
In the case of Apache, the SSL/TLS configuration is stored in /etc/apache2/mods-enabled/ssl.conf.
If you use Let's Encrypt, the configuration may reside in /etc/letsencrypt/options-ssl-apache.conf.
To enable only acceptable cipher suites with high encryption and current protocols set:
SSLProtocol all -SSLv3 -TLSv1 -TLSv1.1
SSLCipherSuite ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256
SSLHonorCipherOrder on
SSLCompression off
Then it would be best if you reloaded the Apache server configuration for the new settings to take effect.
Note that this action limits the eligible default cipher suites and protocol versions to recent Transport Layer Security versions, which might lead users with older browsers to lose access.
Nginx
For Nginx, update the configuration file which is usually located at /etc/nginx/nginx.conf, /etc/nginx/sited-enabled/yoursite.com (Ubuntu/Debian) or /etc/nginx/conf.d/nginx.conf (RHEL/CentOS).
Add the following directive to the server section:
ssl_protocols TLSv1.2;
ssl_ciphers 'ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-SHA38';
ssl_prefer_server_ciphers on;
Restart the Nginx server. This limits the cipher suites and protocol version to recent Transport Layer Security versions. Users with older browsers may lose access.