Prevent Ticketbleed attacks
The proprietary F5 TLS stack is vulnerable to Ticketbleed. It exposes 31 bytes per request to the attacker and ultimately invalidates the encryption.
Security Assessment
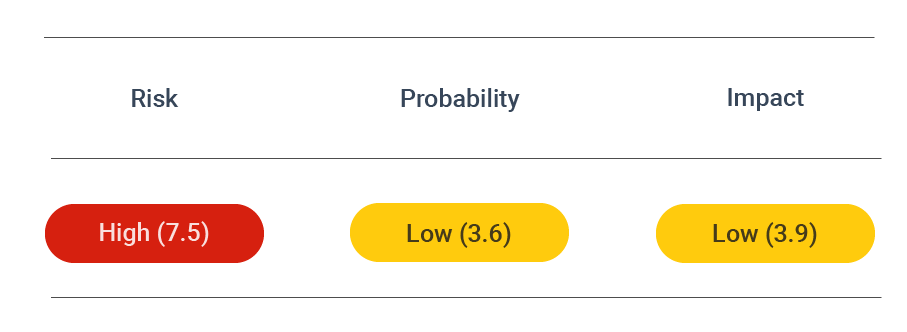 CVSS vector: AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N
CVSS vector: AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N
Vulnerability information
The Ticketbleed vulnerability (CVE-2016-9244) was discovered by Filippo Valsorda in 2017 while examining a bug report from a customer using an F5 load balancer between their server and the Cloudflare Railgun. This software vulnerability affects the implementation of session tickets in the TLS/SSL stack of F5 appliances, such as a BIG-IP virtual server. It specifically applies to those appliances with the non-default session ticket option enabled.
Session tickets are used during the handshake between client and server. Along with the ClientHello, the client sends a session ticket to the server to resume a previous session rather than negotiate a new one. Along with encrypted key material of a prior connection, the session ticket includes a session ID which the server is supposed to echo back to the client to confirm the ticket acceptance and the session resumption.
Filippo found that the resumption technique failed because the F5 device assumed that the session ID had to be of a certain length. Session IDs can be between 1 and 31 bytes long, yet the F5 devices would always echo back 32 byte IDs. The F5 server would pad the ID to its maximum length instead of returning the same ID to the client. This would confuse the client and cause a bug.
The problem is that instead of random padding, the server would send unallocated or uninitialized memory in its response. In other words, the server would inadvertently reveal data that could be sensitive.
An attacker could deliberately send a 1-byte session ID to trick the server into returning 31 bytes of memory.
Prevent attacks
To prevent Ticketbleed, you must either upgrade the version of your appliance or change its settings.
A complete list of the affected versions of appliances can be found on the F5 website. These are primarily versions 12.0.0-12.1.2, and 11.4.0-11.6.1. Therefore, if you have a device running a version known to be vulnerable, you must upgrade it to one known to be without the vulnerability.
Some appliances do not have newer versions, so it may not be possible to upgrade to a non-vulnerable version. In this case, you can mitigate the issue by disabling the session ticket option. Though this solves the problem entirely, it introduces performance degradation because sessions cannot be resumed.
To disable session tickets, follow the instructions provided by F5:
- Sign in to the Configuration utility.
- Go to Local Traffic > Profiles > SSL > Client.
- Select the Advanced configuration option.
- Uncheck the session ticket box to disable the feature.
- Select Update to apply the changes.
Disabling session tickets should not have any adverse effects on your system.