Prevent SSL CRIME attacks
The CRIME (Compression Ratio Info-leak Made Easy) attack is a vulnerability in the SSL compression. The attack against secret web cookies sent over compressed HTTPS or SPDY connections leaves cookie data vulnerable to session hijacking.
Security assessment
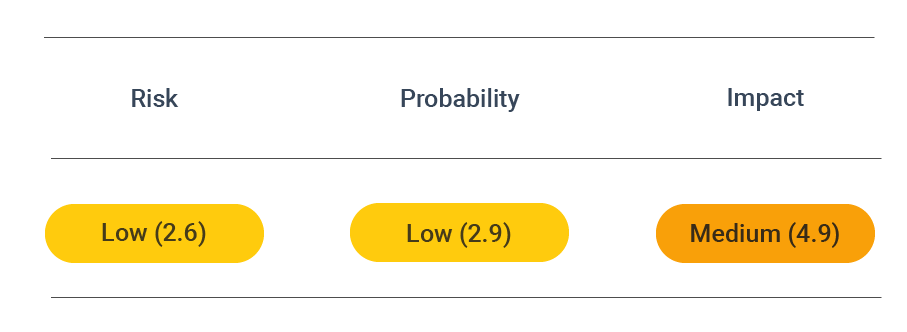
CVSS vector: AV:N/AC:H/AU:N/C:P/I:N/A:N
Vulnerability information
The CRIME attack can be executed against SSL/TLS protocols and the SPDY protocol to hijack users' session cookies while still authenticating to a website.
This can be possible only if the protocols have enabled certain types of data compression methods. While compression can be pretty handy in general, it poses the risk of unintentionally revealing clues about the content of the encryption. In particular, the TLS DEFLATE compression scheme was found to be problematic. Its compression algorithm eliminates duplicate strings.
The CRIME technique was categorized as CVE-2012-4929 by MITRE.
Prevent attacks
To prevent the CRIME vulnerability, disable SSL compression.
Apache
Using the standard settings, CRIME is only a problem for Apache version 2.4.3. To disable SSL compression, define the following directive in your SSL settings (usually /etc/apache2/mods-enabled/ssl.con for /etc/letsencrypt/options-ssl-apache.conf when using Let's Encrypt). Also, you should strongly think of upgrading Apache to the latest version.
SSLCompression off
Nginx
Nginx is vulnerable to CRIME in older versions, with SSL compression enabled. You must update to a recent version of Nginx and OpenSSL. The following versions are known to prevent vulnerability:
- 1.0.9 (if OpenSSL 1.0.0+ used)
- 1.1.6 (if OpenSSL 1.0.0+ used)
- 1.2.2
- 1.3.2
apt-get update; apt-get upgrade # Debian / Ubuntu
yum update # RHeL / CentOS
pacman -Syu # Arch Linux