Prevent SSL BEAST attacks
A server vulnerable to BEAST (Browser Exploit Against SSL/TLS) has the problem: By using weaknesses in cipher block chaining, an attacker can use a Man-In-The-Middle attack to decrypt and obtain authentication tokens.
Security Assessment
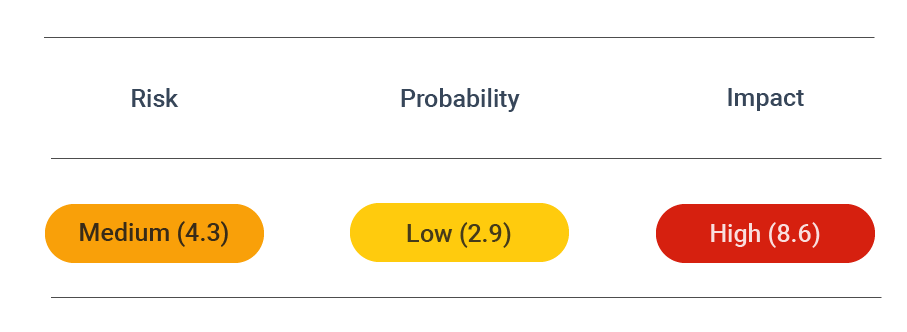
CVSS vector: AV:N/AC:M/Au:N/C:P/I:N/A:N
Vulnerability information
A server using TLS 1.0 with block ciphers is vulnerable to BEAST. This is due to the inherent weakness in CBC that allows attackers to act as a man-in-the-middle and execute the remaining attacks.
For BEAST to be possible, several conditions need to be met:
- An attacker must be able to monitor or sniff the network connection and the sessions between client and server
- A vulnerable version such as TLS 1.0 or an older SSL protocol must be in use (or a downgrade must be possible) with a block cipher
- An applet or JavaScript injection must be likely, overriding the same-origin policy of a website
Due to the specific conditions required to launch BEAST, it is improbable to succeed. It is, therefore, not a particularly practical attack. Furthermore, web applications are now protected by default due to the same-origin policy in modern browsers. Unless the policy is somehow circumvented, such as with server-side CORS headers or another way, performing an injection will be impossible.
That said, it is not entirely inconceivable that this attack could be executed, especially on legacy systems found on organizational intranets. Besides that, it is also helpful to be aware of BEAST for the simple fact of understanding how attackers can use a multi-pronged approach and underscore the need for timely patching and measures.
Prevent attacks
Initially, switching to the RC4 stream cipher was recommended to prevent the vulnerabilities associated with CBC in TLS quickly. But in 2013, the RC4 cipher was found unsafe in many ways. So two years later, its use in TLS implementations was prohibited.
Currently, the simplest and most efficient way of preventing a BEAST attack is to turn off and disable support for TLS 1.0 and 1.1 and SSL on your server. Doing this also protects you from other security flaws that exploit vulnerabilities in SSL and earlier versions of TLS, such as POODLE or DROWN.
To learn how to disable older versions of SSL and TLS, see Secure TLS configurations page.